Your security team is drowning in 11,000 alerts daily.
AI cybersecurity solutions change the math by using machine learning and behavioral analytics to detect, prioritize, and respond to threats faster than human analysts can process them. This guide covers the 10 leading platforms for enterprise security in 2026, with detailed comparisons, evaluation criteria, and implementation best practices to help you choose the right fit for your environment.
What's inside
This guide covers the leading AI cybersecurity solutions built for enterprise environments in 2026. You'll find:
- A clear definition of what AI cybersecurity solutions actually do
- The core benefits these platforms deliver to security teams
- A breakdown of platform types (endpoint, SIEM, cloud, network, application)
- Key applications from phishing detection to automated incident response
- A comparison table of 10 tools with pricing and ratings
- Detailed profiles of each solution with strengths and use cases
- Evaluation criteria and implementation best practices
TL;DR
- AI cybersecurity solutions use machine learning and behavioral analytics to detect, prioritize, and respond to threats faster than rule-based systems
- Platform categories include endpoint protection (CrowdStrike, SentinelOne), SIEM/SOAR (Microsoft Sentinel, Splunk, IBM QRadar), cloud security, and network detection (Vectra AI, Darktrace)
- Key evaluation criteria: environment coverage, integration depth, risk prioritization accuracy, and total cost of ownership
- Primary benefit: real-time threat response with reduced manual effort for security operations teams
- Implementation approach: start with a pilot program, maintain human oversight for critical decisions, and continuously tune models as threats evolve
What are AI cybersecurity solutions
AI cybersecurity solutions use machine learning, behavioral analytics, and automation to detect, prevent, and respond to threats in real time across networks, clouds, and endpoints. Unlike traditional security tools that rely on known attack signatures, AI powered platforms analyze patterns in user behavior, network traffic, and system activity to identify anomalies that signal potential threats.
The shift matters because attackers now use AI themselves and fuel 72% AI assisted attack growth.
Here's how AI powered security platforms work:
- Pattern recognition: ML models identify complex attack signatures by analyzing millions of data points across your environment
- Behavioral baselining: Systems establish what "normal" looks like for users, devices, and applications, then flag deviations instantly
- Automated response: When threats are detected, tools can isolate compromised devices, block malicious traffic, or quarantine files without waiting for human approval
- Continuous learning: Models improve over time as they process new threat data and feedback from security analysts
The practical result? Your security team spends less time chasing false positives and more time investigating validated threats.
Benefits of AI powered security tools
Faster threat detection and response
Traditional security operations centers face a volume problem. The average enterprise generates thousands of security alerts daily, and human analysts can only process so many. AI changes the math by analyzing data at machine speed.
The difference shows up in Mean-Time-to-Respond (MTTR), the key metric security teams track. Catching a breach 100 days faster often determines whether an incident stays contained or spreads across your environment.
Reduced alert fatigue for security teams
Alert fatigue is real. When analysts see hundreds of low-priority notifications, they start ignoring them. AI-powered triage prioritizes validated risks so your team focuses on what matters.
The goal isn't fewer alerts. It's fewer irrelevant alerts.
Improved accuracy and fewer false positives
Rule-based detection systems flag anything that matches a pattern, even if the context makes it harmless. ML models learn context. They understand that a developer downloading large files at 2 AM might be normal, while the same behavior from an HR account is suspicious.
This contextual awareness reduces false positives significantly, freeing security teams from investigating benign events.
Better scalability for enterprise environments
Your attack surface keeps expanding. Cloud workloads, remote endpoints, SaaS applications, IoT devices. Hiring enough analysts to monitor everything manually isn't realistic.
AI handles expanding environments without proportional headcount increases. One platform can monitor millions of events across hybrid infrastructure that would require dozens of analysts to cover manually.
Enhanced compliance and audit support
Continuous monitoring and automated logging support regulatory requirements like SOC 2, GDPR, and HIPAA. AI tools maintain detailed audit trails and can generate compliance reports automatically, reducing the manual burden on security teams during audits.
Types of AI powered security platforms
Understanding platform categories helps you identify which tools fit your specific gaps. Most enterprises deploy multiple types across their environment.
AI powered application security
Application security tools scan code, dependencies, and runtime environments for vulnerabilities. They're essential for organizations practicing DevSecOps or "shift-left" security testing.
These platforms identify issues like insecure code patterns, vulnerable open-source libraries, and misconfigurations before applications reach production.
AI powered endpoint protection
Endpoint Detection and Response (EDR) platforms protect computers, servers, and mobile devices from malware, ransomware, and sophisticated attacks. Unlike traditional antivirus that relies on signature matching, AI-powered EDR detects file-less malware and zero-day threats through behavioral analysis.
When an endpoint starts behaving unusually (encrypting files rapidly, connecting to unknown servers, or escalating privileges), EDR tools detect and contain the threat automatically.
AI driven SIEM and SOAR platforms
Security Information and Event Management (SIEM) platforms aggregate and correlate security events from across your enterprise. Security Orchestration, Automation, and Response (SOAR) adds automated playbooks that respond to common threat patterns.
Together, SIEM and SOAR provide a central nervous system for security operations. AI enhances both by prioritizing alerts, suggesting investigation paths, and automating routine response actions.
AI based cloud security solutions
Cloud security platforms connect code, infrastructure, and runtime to visualize risks across hybrid environments. They map relationships between resources, identify misconfigurations, and prioritize vulnerabilities based on actual exploitability.
The "code-to-cloud" approach matters because a vulnerability in a development environment might be low priority, while the same issue in a production system with internet exposure is critical.
AI powered network detection and response
Network Detection and Response (NDR) platforms monitor network traffic for lateral movement, command-and-control communications, and sophisticated attacks that bypass perimeter defenses. NDR is particularly valuable for detecting threats that have already breached initial defenses and are moving through your environment.
Platform Type | Primary Focus | Best For | Key Capabilities |
|---|---|---|---|
Application Security | Code and dependencies | DevSecOps teams | Vulnerability scanning, supply chain protection |
Endpoint Protection | Devices and servers | IT security teams | Malware detection, automated remediation |
SIEM/SOAR | Event correlation | Security operations | Alert aggregation, automated playbooks |
Cloud Security | Cloud infrastructure | Cloud and DevOps teams | Misconfiguration detection, risk prioritization |
Network Detection | Network traffic | Enterprise security | Lateral movement detection, traffic analysis |
Key applications of cybersecurity AI tools
Phishing detection and prevention
AI analyzes communication patterns to identify spear-phishing attacks that bypass traditional email filters. Modern phishing detection examines writing style, sender behavior patterns, and contextual signals (like unusual requests or timing) rather than just scanning for known malicious links.
Behavioral analytics and anomaly detection
Systems baseline normal user and device behavior, then instantly detect unusual actions. This catches insider threats, compromised credentials, and attackers who have stolen legitimate access.
If an employee's account suddenly accesses files they've never touched, logs in from an unusual location, or transfers large amounts of data, behavioral analytics flags it immediately.
Vulnerability management and prioritization
Not all vulnerabilities are equal. AI triages them by exploitability, exposure, and business context rather than raw CVSS scores. A critical vulnerability on an isolated test server matters less than a medium vulnerability on your customer-facing payment system.
Automated incident response
AI can isolate compromised devices, block malicious traffic, and stop malware spread without waiting for human approval. For common, well-understood threats, automated response dramatically reduces dwell time.
The key is configuring appropriate guardrails. Automated responses work well for clear-cut threats, while ambiguous situations still benefit from human judgment.
Identity and access management
AI monitors authentication patterns to detect credential abuse and restrict unauthorized access. Unusual login times, impossible travel (logging in from two distant locations within minutes), and abnormal access patterns all trigger alerts or automatic session termination.
Comparison table
# | Product | Platform Type | Key Differentiation | Pricing Model | G2 Rating |
|---|---|---|---|---|---|
1 | CrowdStrike Falcon | Endpoint + SIEM | AI-native architecture with threat intelligence | Per endpoint/year | 4.7/5 |
2 | Microsoft Sentinel | Cloud SIEM | Native Azure integration, Security Copilot AI | Usage-based (GB ingested) | 4.4/5 |
3 | Darktrace | Network + Endpoint | Self-learning AI, autonomous response | Quote-based enterprise | 4.4/5 |
4 | SentinelOne Singularity | Unified XDR | Autonomous remediation, single agent | Per endpoint/year | 4.7/5 |
5 | Palo Alto Cortex XDR | Extended Detection | Integration with Palo Alto ecosystem | Quote-based enterprise | 4.5/5 |
6 | Splunk Security Cloud | SIEM + Analytics | Data flexibility, extensive integrations | Usage-based | 4.3/5 |
7 | IBM QRadar | SIEM + SOAR | Watson AI, compliance focus | Quote-based enterprise | 4.2/5 |
8 | Vectra AI | Network Detection | Signal prioritization, hybrid coverage | Quote-based enterprise | 4.6/5 |
9 | Fortinet FortiAI | Integrated Fabric | Consolidated network + endpoint | Per device/year | 4.5/5 |
10 | Elastic Security | Open Platform | Free core features, flexibility | Usage-based + free tier | 4.4/5 |
Top 10 AI cybersecurity solutions for enterprise security
These platforms represent the leading AI powered cybersecurity solutions across platform categories. Each serves different use cases and environments, so the right choice depends on your existing infrastructure and primary security gaps.
1. CrowdStrike Falcon
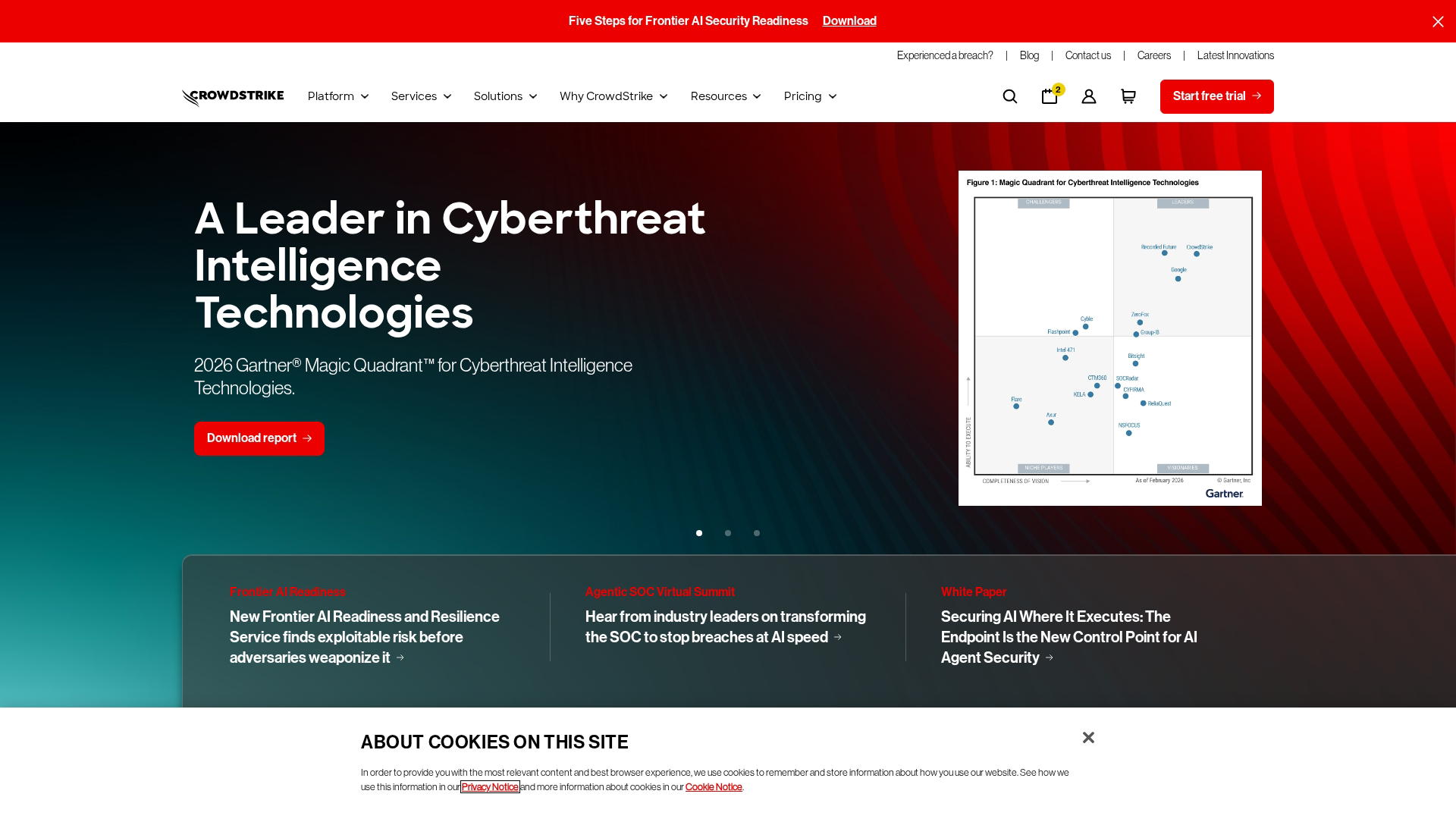
CrowdStrike built its platform as AI-native from the start, not as an add-on to legacy architecture. The Falcon platform combines endpoint protection, threat intelligence, and next-gen SIEM capabilities in a cloud-delivered model that requires no on-premises infrastructure.
Best for: Organizations prioritizing endpoint security and threat hunting with minimal deployment complexity.
Key strengths
- AI-native detection: The platform's ML models analyze billions of events daily across CrowdStrike's customer base, improving detection for everyone
- Threat intelligence: The Threat Graph correlates data across endpoints globally, identifying attack patterns before they reach your environment
- Cloud-delivered: No hardware to deploy or maintain, with updates pushed automatically
Why choose CrowdStrike?
CrowdStrike works well for organizations that want best-in-class endpoint protection without building extensive in-house security operations. The platform's single lightweight agent covers prevention, detection, and response. Implementation typically takes days rather than months.
Pricing: Per-endpoint annual licensing. Falcon Go starts around $59.99/device/year for basic protection. Enterprise tiers with full XDR capabilities require custom quotes.
2. Microsoft Sentinel
Microsoft Sentinel is a cloud-native SIEM built on Azure that integrates with HubSpot, Salesforce, and more across the Microsoft security ecosystem. The addition of Security Copilot brings generative AI capabilities for natural language queries and automated investigation.
Best for: Organizations already invested in Microsoft 365 and Azure who want unified security visibility.
Key strengths
- Native integrations: Seamless connection with Defender products, Azure AD, and Microsoft 365 means faster deployment and richer data
- Security Copilot: Ask questions in plain English like "Show me all failed login attempts from unusual locations this week" and get actionable results
- Scalable pricing: Pay only for data ingested, with free data sources for Microsoft products
Why choose Microsoft Sentinel?
If your organization runs on Microsoft infrastructure, Sentinel provides the fastest path to comprehensive security visibility. The learning curve is lower for teams already familiar with Azure, and the cost model favors organizations with significant Microsoft data sources.
Pricing: Usage-based at approximately $2.46 per GB ingested. Microsoft 365 and Azure activity logs are free. Commitment tiers offer discounts for predictable volumes.
3. Darktrace
Darktrace pioneered self-learning AI that detects novel threats without relying on signatures or rules. The platform learns what's normal for your specific environment, then identifies deviations that signal potential attacks.
Best for: Organizations concerned about unknown threats, insider risks, and sophisticated attackers who evade traditional detection.
Key strengths
- Self-learning AI: The system builds a unique model of your environment within days, no manual configuration required
- Autonomous response: Antigena can take targeted action (slowing connections, blocking specific activities) without disrupting normal operations
- Coverage breadth: Monitors network, email, cloud, endpoints, and OT/IoT from a single platform
Why choose Darktrace?
Darktrace excels at detecting threats that other tools miss because they don't match known patterns. The autonomous response capability is particularly valuable for organizations with limited security staff who can't monitor alerts 24/7.
Pricing: Quote-based enterprise licensing. Expect significant investment for full deployment, typically starting in six figures annually for mid-sized enterprises.
4. SentinelOne Singularity
SentinelOne delivers unified endpoint, cloud, and identity protection through a single agent and console. The platform emphasizes autonomous operation, automatically remediating threats without requiring analyst intervention.
Best for: Organizations wanting consolidated XDR capabilities with minimal manual effort.
Key strengths
- Autonomous remediation: The platform can automatically kill malicious processes, quarantine files, and roll back changes without human approval
- Single agent architecture: One lightweight agent covers prevention, detection, response, and forensics
- Storyline technology: Automatically reconstructs attack chains, showing exactly how threats entered and spread
Why choose SentinelOne?
SentinelOne works well for organizations that want to reduce manual security operations. The autonomous capabilities mean threats get contained even when analysts aren't watching, and the single-agent approach simplifies deployment and management.
Pricing: Per-endpoint annual licensing. Core protection starts around $45/endpoint/year. Complete and Enterprise tiers with full XDR capabilities require custom quotes.
5. Palo Alto Networks Cortex XDR
Palo Alto Cortex XDR extends detection and response across endpoints, network, and cloud. The platform integrates tightly with Palo Alto's broader security portfolio, including next-gen firewalls and Prisma Cloud.
Best for: Organizations with existing Palo Alto infrastructure who want unified visibility across their security stack.
Key strengths
- Cross-domain correlation: Combines endpoint, network, and cloud data for comprehensive threat detection
- Behavioral analytics: ML models identify threats based on behavior patterns rather than signatures
- Integration depth: Native connection with Palo Alto firewalls, Prisma Access, and Prisma Cloud
Why choose Cortex XDR?
If you're already running Palo Alto firewalls or Prisma Cloud, Cortex XDR provides the most seamless path to extended detection and response. The platform leverages data from your existing Palo Alto investments to improve detection accuracy.
Pricing: Quote-based enterprise licensing. Pricing depends on endpoints covered and integration with other Palo Alto products.
6. Splunk Security Cloud
Splunk remains the industry standard for security analytics, with unmatched flexibility in data ingestion and analysis. The platform handles structured and unstructured data from virtually any source, making it ideal for complex, multi-vendor environments.
Best for: Organizations with diverse security tools that need a central analytics platform with maximum flexibility.
Key strengths
- Data flexibility: Ingest and analyze data from any source, regardless of format or vendor
- Search and investigation: Splunk's query language (SPL) enables deep forensic investigation
- Extensive ecosystem: Thousands of apps and integrations available through Splunkbase
Why choose Splunk?
Splunk works well for organizations with mature security operations who need maximum flexibility and analytical depth. The platform's learning curve is steeper than alternatives, but the capabilities are unmatched for complex investigations.
Pricing: Usage-based pricing by data volume ingested. Workload pricing options available for predictable costs. Enterprise deployments typically start at $150,000+ annually.
7. IBM QRadar
IBM QRadar combines SIEM capabilities with Watson AI for threat intelligence and investigation assistance. The platform emphasizes compliance and is particularly strong in regulated industries like financial services and healthcare.
Best for: Large enterprises needing comprehensive compliance support and integration breadth.
Key strengths
- Watson integration: AI assists with threat investigation, suggesting next steps and correlating indicators
- Compliance focus: Pre-built reports and dashboards for major regulatory frameworks
- Network insights: Deep packet inspection and flow analysis for network-level visibility
Why choose IBM QRadar?
QRadar fits organizations in regulated industries who need strong compliance capabilities alongside threat detection. The platform's maturity and IBM's enterprise support make it a safe choice for risk-averse organizations.
Pricing: Quote-based enterprise licensing. Pricing depends on events per second (EPS) and flows per minute (FPM). Cloud and on-premises deployment options available.
8. Vectra AI

Vectra AI focuses specifically on network detection and response, using AI to identify attackers moving through your environment. The platform excels at detecting threats that have bypassed perimeter defenses.
Best for: Organizations needing visibility into lateral movement and sophisticated attacks across hybrid networks.
Key strengths
- Signal prioritization: AI ranks threats by severity and certainty, reducing alert noise significantly
- Hybrid coverage: Monitors on-premises networks, cloud environments, and SaaS applications
- Attack progression tracking: Visualizes how threats move through your environment over time
Why choose Vectra AI?
Vectra works well for organizations concerned about sophisticated attackers who have already breached initial defenses. The platform's focus on network behavior makes it complementary to endpoint-focused tools.
Pricing: Quote-based enterprise licensing. Pricing depends on network coverage and deployment scope.
9. Fortinet FortiAI
Fortinet integrates AI-driven threat detection across its Security Fabric, providing consolidated protection for network, endpoint, and cloud. The approach emphasizes operational simplicity through a unified platform.
Best for: Organizations wanting consolidated network and endpoint security from a single vendor.
Key strengths
- Security Fabric integration: AI capabilities span firewalls, endpoints, email, and cloud
- FortiGuard threat intelligence: Global threat research feeds real-time updates to all products
- Operational simplicity: Single management console for multiple security functions
Why choose Fortinet?
Fortinet fits organizations that prefer vendor consolidation over best-of-breed approaches. The integrated platform reduces complexity and can lower total cost of ownership compared to managing multiple point solutions.
Pricing: Per-device annual licensing. Pricing varies by product and deployment size.
10. Elastic Security
Elastic Security provides SIEM, endpoint, and cloud security on the open Elastic Stack. The platform offers free core features with paid tiers for advanced capabilities, making it accessible for organizations with limited budgets.
Best for: Organizations wanting flexibility, control, and cost-effective security analytics.
Key strengths
- Open platform: Built on open-source Elastic Stack with no vendor lock-in
- Free tier: Core SIEM and endpoint capabilities available at no cost
- Scalability: Handles massive data volumes efficiently
Why choose Elastic Security?
Elastic works well for organizations with technical expertise who want maximum control over their security platform. The free tier provides genuine value, and the open architecture avoids vendor lock-in concerns.
Pricing: Free tier available with core features. Paid tiers (Standard, Gold, Platinum, Enterprise) add advanced features and support. Cloud pricing starts around $95/month for basic deployments.
How to evaluate AI powered cybersecurity tools
1. Assess coverage across your environment
Map your attack surface before evaluating tools. Consider endpoints (laptops, desktops, servers, mobile devices), cloud workloads (AWS, Azure, GCP), network infrastructure, applications (SaaS tools, custom applications, APIs), and identity systems (Active Directory, cloud identity providers).
Verify that candidate tools cover your specific environment. A platform that excels at cloud security won't help if your primary risk is endpoint compromise.
2. Examine risk prioritization capabilities
Ask vendors how their platform prioritizes alerts. Look for contextual scoring that considers business impact, not just technical severity. Request sample alert data showing how the platform would handle realistic scenarios in your environment.
3. Validate integration with your security stack
AI cybersecurity tools work best when they connect to your existing infrastructure. Key integration points include SIEM/SOAR systems, ticketing platforms like ServiceNow or Jira, identity providers, and communication tools like Slack or Teams.
When communicating security capabilities to stakeholders, interactive demos can help marketing teams and pre-sales teams showcase complex security features without requiring live environment access.
4. Review remediation and response workflows
Evaluate whether the tool provides automated response for clear-cut threats, guided remediation with specific steps for analysts, rollback capabilities if automated response causes problems, and customizable playbooks for your specific environment.
5. Measure scalability and compliance support
Consider future growth and regulatory requirements. How does pricing scale as your environment grows? What compliance frameworks does the platform support (SOC 2, GDPR, HIPAA, PCI-DSS)? Can the platform handle your projected data volumes in 2-3 years?
Challenges and risks of AI in cybersecurity
Adversarial attacks on AI models
Attackers can manipulate AI systems through poisoned training data or adversarial inputs designed to evade detection. Organizations deploying AI security tools can verify that vendors test for adversarial robustness and update models regularly.
Data quality and training requirements
AI models are only as good as their training data. Poor quality data, incomplete coverage, or biased samples lead to missed threats or excessive false positives. Ensure your environment provides sufficient data for models to learn effectively.
Over-reliance on automation
Automated response works well for common, well-understood threats. But novel attacks and ambiguous situations still benefit from human judgment. Configure appropriate guardrails and maintain analyst oversight for high-impact decisions.
Explainability and trust gaps
Security teams sometimes struggle to understand why AI flagged certain events. This "black box" problem can undermine trust and make it harder to tune systems effectively. Look for platforms that provide clear explanations for their decisions.
Implementation complexity and cost
Enterprise AI security tools require significant investment in deployment, tuning, and ongoing maintenance. Budget for professional services, training, and the time your team will spend learning new platforms.
Best practices for implementing AI security tools
1. Start with a pilot program
Deploy in a limited environment to validate detection accuracy before enterprise rollout. Choose a representative segment of your infrastructure and run the tool in monitoring mode before enabling automated response.
2. Maintain human oversight in critical decisions
Keep humans in the loop for high-impact response actions like quarantining production systems or blocking executive accounts. Automated response works well for endpoints and known threat patterns, but critical infrastructure decisions benefit from human judgment.
3. Ensure quality training data
AI security tools learn from your environment. Clean, representative data improves detection accuracy. Invest in data hygiene as an ongoing requirement, not a one-time setup task.
4. Integrate AI tools with existing workflows
Connect new tools to existing SIEM, ticketing, and communication systems. Security tools that exist in isolation create blind spots and extra work for analysts.
5. Continuously monitor and tune AI models
AI requires ongoing validation and adjustment as threats evolve and environments change. Schedule regular reviews of detection accuracy, false positive rates, and response effectiveness. Update models and rules based on what you learn.
How generative AI is changing cybersecurity
Threat intelligence synthesis
Generative AI summarizes threat reports and correlates indicators across sources, giving analysts faster context. Instead of reading dozens of reports, analysts can ask questions and get synthesized answers about emerging threats.
Natural language security queries
Security teams can ask questions in plain English instead of writing complex queries. Microsoft Security Copilot reflects 55% deploying AI copilots, letting analysts type "Show me all suspicious PowerShell activity this week" and get actionable results.
Automated playbook generation
AI can draft response playbooks based on incident type and organizational context. This accelerates the creation of standardized procedures and helps less experienced analysts follow best practices.
Agentic AI for autonomous response
Agentic AI refers to autonomous agents that can investigate and respond to incidents with minimal human intervention. This emerging capability promises to handle routine incidents end-to-end, freeing analysts for complex investigations.
Considerations for choosing AI cybersecurity solutions
Before making a final decision, work through this checklist:
- Environment fit: Does the tool cover your attack surface (cloud, on-prem, hybrid)?
- Integration depth: Can you connect to existing SIEM, SOAR, and ticketing systems?
- Detection accuracy: What is the false positive rate and how does the vendor validate it?
- Response capabilities: Does the tool offer automated or guided remediation?
- Vendor stability: Is the vendor established with ongoing product investment?
- Total cost of ownership: Consider licensing, implementation, training, and ongoing maintenance
Tip: Request a proof-of-concept deployment in your actual environment. Vendor demos show best-case scenarios. Real-world testing reveals how the tool handles your specific data and threat landscape.
Strengthen your security posture with AI powered tools
AI cybersecurity solutions provide faster detection, reduced analyst burden, and improved coverage across enterprise environments. The platforms covered here represent the leading options across endpoint protection, SIEM/SOAR, cloud security, and network detection. For teams evaluating these solutions, presales software tools can help streamline the demonstration and evaluation process.
Start with an assessment of your current gaps. Where are threats most likely to enter? Where do you lack visibility? Which platform category addresses your primary risk?
Then pilot one platform before broader deployment. Validate detection accuracy in your environment, test integrations with your existing tools, and ensure your team can operate the platform effectively.
Start your journey with Guideflow today!
FAQs about AI cybersecurity solutions
How long does it take to implement an enterprise AI cybersecurity solution?
Implementation timelines vary from weeks to months depending on environment complexity, integration requirements, and deployment scope. Most organizations start with pilot programs in limited environments before rolling out enterprise-wide.
What training data does an AI security tool require to be effective?
AI security tools need historical security logs, network traffic data, and baseline user behavior data to train detection models. Data quality directly impacts detection accuracy, so organizations with clean, comprehensive logs see better results.
Can AI cybersecurity solutions fully replace human security analysts?
No. AI augments human analysts by handling routine triage and initial investigation, but critical decisions and complex investigations still require human expertise. The goal is to make analysts more effective, not to eliminate them.
How do AI powered security tools detect zero-day threats without signatures?
AI models identify threats through behavioral anomalies and pattern recognition rather than known signatures. When a process behaves unusually (even if it's never been seen before), behavioral analysis flags it for investigation.
Are AI cybersecurity solutions suitable for mid-sized businesses or only large enterprises?
Cloud-delivered AI security tools have made advanced capabilities accessible to mid-sized businesses. Platforms like CrowdStrike, SentinelOne, and Elastic Security offer entry-level tiers that provide genuine protection without enterprise-scale investment.












